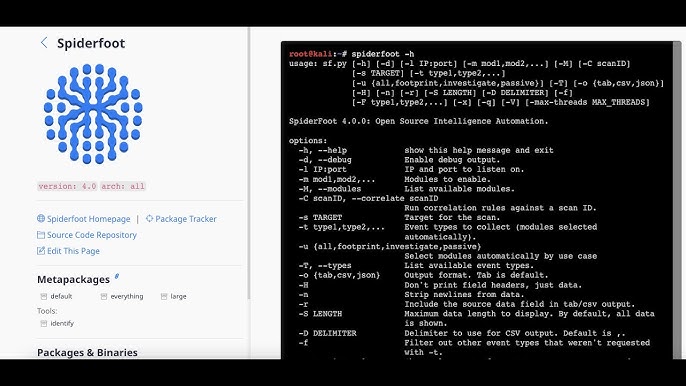
SpiderFoot is one of the most powerful OSINT automation frameworks designed to collect intelligence from hundreds of data sources. Its flexibility and wide module support allow it to analyze a broad range of digital targets. Whether used for security assessments, reconnaissance, or exposure analysis, SpiderFoot can extract deep insights from almost any identifier linked to a digital footprint.
SpiderFoot’s strength lies in its ability to automate the discovery of relationships between data points. By scanning IP addresses, domains, email addresses, human names, and even entire networks, the tool helps users identify risks, uncover connections, and understand the breadth of publicly available information about a target. Its broad scanning capabilities make SpiderFoot a valuable asset for penetration testers, SOC teams, researchers, and investigators.
Understanding SpiderFoot’s Target Scope
Overview of Target Types
SpiderFoot is designed to work with multiple target classes, each representing a different type of digital identity or footprint. These range from technical identifiers such as IP addresses and subnets to personal identifiers like names and email addresses. The tool uses both passive and active data-gathering techniques to ensure a complete intelligence profile.
Why Target Variety Matters
The variety of targets supported by SpiderFoot ensures that users can run investigations from multiple angles. Every data point is interconnected, and analyzing multiple targets often reveals relationships that would otherwise stay hidden. From uncovering hidden systems to mapping attack surfaces, target diversity enhances the accuracy of intelligence collection.
Technical Targets Supported by SpiderFoot
IP Addresses
One of the most commonly analyzed targets in SpiderFoot is an IP address. By scanning an IP, SpiderFoot can identify geolocation, hosting provider, reverse DNS records, open ports, vulnerabilities, running services, and associations with other entities. This helps security professionals understand how an IP operates on the internet and whether it exposes security weaknesses.
IP Ranges and Subnets
SpiderFoot can scan entire subnets or network ranges, making it useful for mapping internal and external network infrastructure. This allows organizations to discover unmanaged assets, rogue systems, and unknown services that could introduce vulnerabilities.
Domain Names
Domains are among the most information-rich targets SpiderFoot can analyze. Scanning a domain allows the tool to gather DNS records, server technologies, SSL details, site metadata, WHOIS data, connected subdomains, hosting history, and blacklists. It can also uncover whether the domain has associations with leaked credentials, malware, or spam activity.
Hostnames
Hostnames often provide deeper technical details about specific devices or servers. SpiderFoot can analyze hostnames to identify services, network paths, historical associations, content fingerprints, and software versions. This helps in pinpointing vulnerabilities tied to specific systems.
Identity-Based Targets
Email Addresses
SpiderFoot can scan email addresses to check for data breaches, associated accounts, credential leaks, social profiles, domain affiliations, and exposure in public records. This helps individuals and organizations assess their online exposure and potential authentication risks.
Person Names
SpiderFoot also supports scanning of human names, which can be useful for digital investigations, background checks, or profiling. The tool may uncover business affiliations, social presence, breach associations, public records, and potential cybersecurity exposure linked to a person’s digital footprint.
Usernames
Usernames are often consistent across platforms. SpiderFoot can analyze usernames to identify connected profiles, online activity traces, forum posts, and breached databases. This is especially useful for investigators tracing threat actors or impersonation attempts.
Organizational Targets
Company Names
SpiderFoot can process organization names to uncover related domains, employee leaks, infrastructure footprints, DNS records, email exposures, and digital vulnerabilities. This makes it useful for companies conducting self-assessments or competitor research.
Registrant Information
Details from WHOIS records can be used as targets themselves. For example, scanning an owner’s name, email, or organization listed in WHOIS can reveal additional domains, IP allocations, or associated online assets.
Network and Infrastructure Targets
Autonomous System Numbers (ASNs)
SpiderFoot supports the scanning of ASNs to map an organization’s public network space. Insight gathered from ASN scans includes allocated IP blocks, routing details, hosting providers, and infrastructure relationships.
Network Blocks
Scanning network blocks allows SpiderFoot to identify active hosts, services, open ports, and exposed systems. This helps organizations discover unmanaged infrastructure and assess attack surfaces more accurately.
BGP Routes
Although less commonly used, SpiderFoot can analyze routing information to provide a broader understanding of internet-level structures and how a target’s network fits into global routing tables.
Web and Application Targets
Websites and Web Servers
SpiderFoot can analyze specific websites to gather details about:
- Web technologies
- SSL certificates
- Page metadata
- Historical snapshots
- Content fingerprints
- Server misconfigurations
- Script dependencies
This enhances web security assessments and exposure analysis.
URLs and Endpoints
By scanning URLs, the tool can identify redirects, tracking scripts, security headers, and endpoint structures that may reveal valuable intelligence for penetration testers.
Digital Asset Exposure Targets
Leaked Credentials
SpiderFoot can analyze leaked credential sets or combinations of data to identify associations, linked domains, and data breach instances where the target may appear.
Database Dumps
If targeted legally and ethically, the tool can process structured data to uncover patterns, relationships, or leaked information relevant to investigations.
Public Document Metadata
SpiderFoot can parse metadata from public documents to extract author information, creation devices, embedded IPs, and other digital identifiers.
Social and Behavioral Targets
Social Media Profiles
SpiderFoot modules can identify associations between usernames, emails, person names, and social media accounts. This is useful for investigators, analysts, and digital profiling.
Online Forums and Communities
The tool can detect usernames or email addresses in public communities, revealing patterns of posting, affiliations, or suspicious interactions.
Malware and Threat Intelligence Targets
Malicious IPs and Domains
SpiderFoot can compare targets against threat intelligence databases to identify malware hosting, botnet associations, spam activity, or blacklisted infrastructure.
Hashes and File Identifiers
Some modules support scanning file hashes to uncover malware records, threat reports, and historical analysis.
Use Cases for Various Target Types
Penetration Testing
Penetration testers use SpiderFoot to automate reconnaissance, revealing targets for deeper exploitation. Domains, IPs, subnets, and URLs are especially valuable for building an attack map.
Vulnerability Assessments
Scanning public assets allows organizations to identify exposed services, outdated software, and risky configurations before attackers do.
Threat Intelligence
Analysts can track malicious actors by analyzing usernames, email addresses, or IP addresses across threat databases and forums.
Digital Investigations
Investigators use SpiderFoot to trace online identities, uncover hidden connections, and create accurate digital profiles.
Brand Protection
Scanning company names, domains, and leaked credentials helps organizations monitor exposure and take preventive measures.
Benefits of SpiderFoot’s Wide Target Support
Comprehensive Reconnaissance
By supporting a wide range of targets, SpiderFoot provides a full picture of a target’s online presence.
Automation of Complex Tasks
Instead of relying on separate tools, SpiderFoot automates the entire intelligence workflow from multiple sources.
Enhanced Accuracy
The interlinking of targets helps uncover patterns that manual research would easily miss.
Versatile Use Cases
SpiderFoot’s target flexibility makes it useful for cybersecurity, risk assessment, digital investigations, and research.
Challenges and Considerations
Large Data Volume
Scanning a wide variety of targets can produce massive amounts of data. Users must filter insights carefully.
Ethical and Legal Boundaries
While SpiderFoot is a powerful tool, users must ensure all scans comply with legal and ethical guidelines.
Data Interpretation Skills
The tool gathers data, but users need analytical skills to interpret findings correctly.
Conclusion
SpiderFoot supports a wide range of targets, making it one of the most versatile OSINT automation tools available today. From domains and IP addresses to personal names, email accounts, organizations, and entire networks, SpiderFoot delivers deep and actionable intelligence. Its ability to correlate data across numerous modules and sources enables investigators, security professionals, and researchers to uncover hidden connections, assess exposure, and map digital footprints with exceptional accuracy.
SpiderFoot continues to evolve, expanding its target capabilities and strengthening its role in modern cybersecurity investigations. The breadth of target types it supports ensures that users can perform comprehensive reconnaissance, improve security posture, and gain a clearer understanding of their digital environment.