SpiderFoot is one of the most versatile and intelligent OSINT automation tools used by cybersecurity professionals across the world. Designed to gather data from hundreds of sources, it offers deep visibility into digital footprints and potential exposure points. Its automated scanning, modular structure, and ability to analyze numerous data types make it valuable for multiple security operations.
In the modern cybersecurity landscape, organizations must understand both how attackers gather information and how they can defend against such reconnaissance. SpiderFoot plays a crucial role in both domains by revealing what is publicly accessible about a target and how this information can be leveraged.
Understanding SpiderFoot as an OSINT Automation Framework
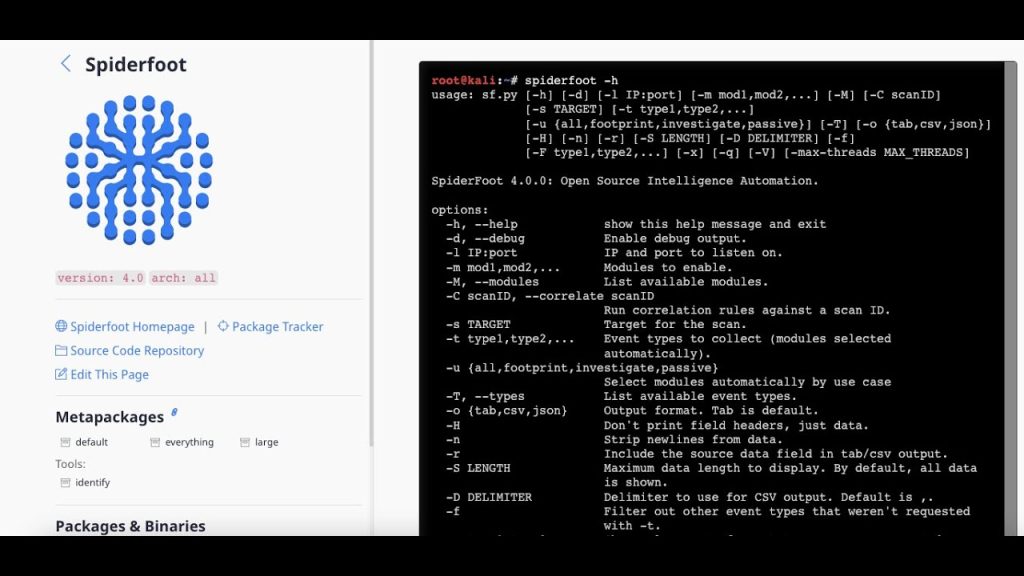
SpiderFoot operates as a highly customizable and automated intelligence-gathering framework. Built in Python and leveraging a wide ecosystem of modules, it collects detailed information about targets such as domains, networks, emails, IP addresses, and individuals. This flexibility allows cybersecurity teams to shape SpiderFoot to fit offensive testing procedures as well as defensive monitoring strategies.
Through active and passive scanning capabilities, users can choose between quiet OSINT collection and active probing. As a result, SpiderFoot becomes a powerful multipurpose tool that aligns with the diverse needs of red teams and blue teams.
What Offensive Security Means in Cyber Operations
Offensive security refers to activities performed to simulate real-world attacks on systems to uncover weaknesses. These tasks are often carried out by penetration testers, red teams, and ethical hackers. The goal is to understand how adversaries gather information and exploit vulnerabilities.
SpiderFoot serves as an essential component in this phase because attackers typically begin with reconnaissance. Before exploiting a system, they collect every available detail, map exposed services, identify weak points, and build a complete profile of their target. SpiderFoot automates this initial phase, giving ethical hackers a realistic picture of how an attacker might begin.
How SpiderFoot Supports Offensive Security Activities
SpiderFoot integrates with more than two hundred data sources, allowing penetration testers to discover sensitive information quickly. For offensive use, it can uncover:
- Exposed credentials
- Open ports and services
- Domain ownership details
- DNS records
- Leaked data
- Publicly available email addresses
- Infrastructure mapping
These findings help testers understand how much information an attacker could gather without interacting directly with the target.
Active scanning modules allow SpiderFoot to perform more aggressive checks, such as probing services and collecting responses. Ethical hackers combine this data with manual testing to design realistic attack paths. By revealing open attack surfaces, SpiderFoot directly contributes to validating the strength of a system before attackers exploit it.
Offensive Reconnaissance with Automation
Traditional reconnaissance requires multiple tools and time-consuming manual searches. SpiderFoot centralizes the process, running automated scans that may take hours to perform manually. Offensive teams benefit from this automation because it enables:
- Faster intelligence collection
- Deep visibility into target infrastructure
- Improved mapping of possible exploitation paths
- Comprehensive enumeration of digital assets
Automation ensures consistency and accuracy, which is essential for professionally conducted penetration tests.
What Defensive Security Means in Cyber Monitoring
Defensive security focuses on protecting systems, identifying vulnerabilities, and reducing exposure. Defensive teams include blue teams, SOC analysts, incident responders, and threat analysts. Their role is to identify threats before they escalate and to mitigate weaknesses that attackers may exploit.
SpiderFoot provides defenders with the intelligence required to understand how the organization appears externally. Much like an attacker, the defender uses this information to find weak points before they are abused.
How SpiderFoot Strengthens Defensive Security
For defensive security tasks, SpiderFoot helps security teams detect:
- Misconfigured systems
- Exposed services and outdated technologies
- Public leaks related to corporate data
- Domains impersonating the organization
- Unexpected IP associations
- Shadow infrastructure
- Sensitive information unintentionally available online
By performing these scans regularly, defenders gain a complete view of their external security posture.
Assessing the Organization’s Digital Footprint
A major aspect of defensive work is identifying what attackers can find publicly. SpiderFoot compiles this data and presents it in a clear manner. It shows how much information the organization reveals through public records, social platforms, third-party databases, and DNS information.
Organizations often discover forgotten assets, old servers, or exposed subdomains that pose silent threats. SpiderFoot ensures these weaknesses do not remain hidden.
Reducing Attack Surface through Continuous Monitoring
SpiderFoot scans can be scheduled periodically, giving defenders continuous insight into changes in their digital presence. Continuous monitoring is crucial because new threats may arise as systems evolve.
With automated scanning, defenders can detect newly exposed services, unpatched applications, or unexpected DNS changes. This intelligence allows the security team to respond quickly and reduce the attack surface.
Mapping Third-Party Risks and External Dependencies
Many organizations rely on external services, hosting providers, or partners. SpiderFoot uncovers information related to these connections, helping defenders evaluate third-party risks. By understanding what is exposed through external dependencies, organizations can adjust their security posture accordingly.
Internal vs External Perspective in Security
SpiderFoot focuses on external intelligence. For offensive teams, this external view mirrors what an attacker sees. For defensive teams, it becomes a valuable resource for identifying oversights and unintentional exposures.
Both perspectives rely on the same data but use it for different purposes:
- Offensive teams use it to plan attacks.
- Defensive teams use it to prevent them.
This duality makes SpiderFoot a unique tool in cybersecurity.
Combining SpiderFoot with Other Security Tools
While SpiderFoot is powerful on its own, combining it with other tools increases its effectiveness. Offensive teams may pair it with vulnerability scanners or exploitation frameworks. Defensive teams can integrate its findings into SIEM systems or risk assessment tools.
SpiderFoot provides the intelligence, and other tools provide deeper analysis or response actions. This layered approach enhances both attack simulations and defensive monitoring.
Benefits of Using SpiderFoot for Combined Security Operations
Organizations that use SpiderFoot for both offensive and defensive tasks gain several advantages, such as:
- Comprehensive visibility into external exposure
- Faster discovery of vulnerabilities
- Reduced probability of successful attacks
- Identification of misconfigurations before exploitation
- Better understanding of attacker strategies
- Preparation for realistic penetration testing scenarios
The tool acts as a bridge between offensive and defensive security, enabling both teams to use the same intelligence for different objectives.
Ethical and Legal Considerations
SpiderFoot should always be used responsibly. Offensive testing must be performed with permission, and defensive monitoring should comply with privacy policies. While the tool is powerful, it requires ethical handling to ensure security objectives are met without violating boundaries.
Challenges and Limitations
Although effective, SpiderFoot has some limitations, including:
- Dependency on external data source availability
- Potential false positives during scans
- Limited active scanning depth compared to full penetration tools
These limitations do not reduce its value but highlight the need for complementary tools and human expertise.
Conclusion
SpiderFoot is a highly capable OSINT automation tool that supports both offensive and defensive security operations. Its ability to gather, analyze, and organize intelligence makes it indispensable for penetration testers, red teams, blue teams, and threat analysts. SpiderFoot helps attackers simulate real-world reconnaissance while providing defenders with insights needed to strengthen security controls.
SpiderFoot ultimately enables organizations to understand their digital footprint, reduce exposure, and anticipate potential attack vectors. Its dual-use capabilities make it a strategic asset for building stronger and more resilient cybersecurity systems.