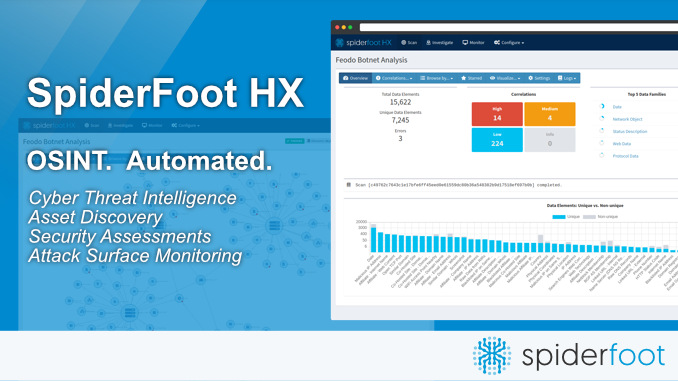
SpiderFoot is one of the most advanced and versatile OSINT automation tools available for cybersecurity professionals, penetration testers, and researchers. Designed to collect intelligence from hundreds of sources, SpiderFoot streamlines the entire reconnaissance workflow. Its modular design allows users to analyze domains, IP addresses, email addresses, hosts, subnets, and other digital entities using a wide range of data sources without switching tools or performing manual research.
In this article, you will learn in depth which data sources SpiderFoot integrates with, how its modules function, why they matter in digital investigations, and how professionals leverage them for both offensive and defensive security operations. This guide provides a complete overview of SpiderFoot’s integration capabilities, making it easier for you to understand the scale, depth, and flexibility of this powerful OSINT framework.
Understanding SpiderFoot’s Integration Architecture
SpiderFoot uses a modular architecture consisting of more than 200 modules, each responsible for interacting with a specific data source or performing a specific type of analysis. These modules cover everything from DNS enumeration to breach detection, email validation, network scanning, threat intelligence checks, and metadata extraction.
Every module works independently but contributes to a unified pool of intelligence. This makes SpiderFoot particularly strong in automated reconnaissance, allowing users to run deep scans without manual intervention.
Categories of Data Sources Integrated with SpiderFoot
SpiderFoot integrates with a wide array of data sources, each falling into well-defined categories. These categories help users understand what type of intelligence they can expect from a given module.
DNS and Network Infrastructure Data
These modules provide foundational technical intelligence. SpiderFoot integrates with DNS records, network lookups, and IP intelligence providers to gather details such as:
- A, AAAA, MX, and TXT records
- Reverse DNS lookups
- Whois lookups
- Autonomous System Numbers
- Network ranges associated with a target
- Hostname resolution
- TTL values and DNS metadata
These integrations are crucial for understanding server configuration, infrastructure relationships, hosting providers, and potential vulnerabilities exposed through DNS.
Search Engine and Web Intelligence Data
SpiderFoot uses multiple search engines and web crawlers to discover publicly indexed information. Modules in this category search for:
- Public mentions of a target
- Subdomains detected through search indexing
- Archived versions of webpages
- Related domains
- Public references on blogs or online forums
These modules help reveal the external footprint of a target, including information unintentionally exposed to the public internet.
Social Media and Public Profile Data
While SpiderFoot does not access private social media data, it can extract publicly available information from:
- Social networks
- Public profiles
- Online identity records
- Employee listings
- Business directories
This makes it easier to enumerate individuals related to an organization, map digital relationships, or collect social intelligence for cybersecurity assessments.
Breach and Credential Leak Databases
SpiderFoot integrates with multiple breach and password leak sources to determine whether sensitive information about a target has been compromised. These modules identify:
- Leaked emails
- Exposed username-password pairs
- Breached datasets
- Compromised credentials related to an organization
This intelligence is critical for defensive cybersecurity, as it helps organizations proactively secure exposed accounts.
Malware and Threat Intelligence Sources
SpiderFoot can query a variety of threat intelligence databases to determine whether:
- A domain has been blacklisted
- An IP address is associated with malicious activity
- A hostname is known for distributing malware
- URLs appear in threat feeds
- Infrastructure belongs to botnets or malicious operators
Threat intelligence modules provide essential visibility when identifying attacker infrastructure or compromised assets.
Geolocation and Hosting Data Providers
SpiderFoot integrates with numerous services that offer network and geolocation intelligence, enabling users to identify:
- Geographic locations of IP addresses
- Country, city, and ISP ownership
- Hosting providers
- Data center information
- Physical server distribution
This type of intelligence helps track infrastructure origins, assess risks, or verify hosting legitimacy.
Certificate Transparency and SSL Data
SpiderFoot includes modules that inspect SSL certificate data. These modules extract:
- Certificate issuers
- Domains listed in certificates
- Expiration dates
- Public certificate logs
- Historical certificate entries
Such intelligence is important for detecting rogue certificates, expired SSL configurations, or domain variations created by attackers.
Dark Web and Deep Web Monitoring
Some SpiderFoot modules interact with deep web or specialized repositories to identify:
- Hidden service mentions
- Illicit marketplace references
- Anonymous posts related to the target
- Forums discussing vulnerabilities or leaked assets
These sources provide deeper intelligence often missed by traditional search engines.
Email and Contact Discovery Sources
SpiderFoot integrates with email verification tools and public contact information databases to gather:
- Employee emails
- Organizational contact patterns
- Email metadata
- Valid and invalid email statuses
This intelligence is valuable for social engineering testing, incident response, and digital profiling.
Metadata and Document Extraction
Several modules extract metadata from:
- Public files
- PDFs
- Images
- Documents
- Archives
These can reveal operational details such as usernames, software versions, authors, and even geolocation coordinates.
Web Application and Technology Fingerprinting
SpiderFoot integrates with multiple sources and scanning techniques to identify:
- Server technologies
- CMS details
- Software versions
- Frameworks used
- Potential vulnerabilities associated with these technologies
This information supports penetration testers in mapping and assessing attack surfaces.
Reputation and Blacklist Data
Modules in this category check various blacklists to determine whether:
- A target’s domain or IP is considered malicious
- Spam reports have been filed
- Domains have been flagged for phishing
- Addresses appear in known malware lists
Blacklist and reputation data help organizations understand how their infrastructure is perceived across the internet.
How SpiderFoot Modules Work During a Scan
SpiderFoot modules run either sequentially or in parallel depending on the configuration. When a module produces data, other relevant modules automatically consume that data to generate additional intelligence. For example:
- A DNS module may discover new subdomains.
- A Whois module may analyze ownership details of those subdomains.
- A threat intelligence module may check those subdomains against blacklists.
- A metadata module may extract file details from discovered URLs.
This chain reaction enables SpiderFoot to perform deep, wide, and highly detailed reconnaissance.
Benefits of SpiderFoot’s Integration with Diverse Data Sources
Automation at Scale
By integrating with hundreds of data sources, SpiderFoot removes the need for manual intelligence gathering. A single automated scan can produce results that would take days to gather manually.
Broad Visibility Across the Internet
From DNS to social networks to threat intelligence feeds, SpiderFoot covers every major area of public and semi-public data, offering unmatched visibility into digital footprints.
Improved Accuracy and Correlation
Modules communicate with each other to cross-verify results, reducing false data and providing multi-angle intelligence.
Deep Reconnaissance Capabilities
SpiderFoot can reveal hidden infrastructure, old domains, leaked employee information, vulnerable servers, and connections not easily spotted through manual research.
Useful for Both Offensive and Defensive Operations
- Offensive teams use SpiderFoot to map an entire target surface.
- Defensive teams use it to find exposures and leaks before attackers do.
This dual capability makes SpiderFoot a highly reliable tool for diverse cybersecurity workflows.
Real-World Use Cases of SpiderFoot Integrations
SpiderFoot’s powerful integrations make it suitable for a variety of tasks, including:
Penetration Testing
Discovering subdomains, infrastructure, open ports, and technical misconfigurations.
Threat Hunting
Identifying malicious behavior, compromised servers, and threat indicators.
Vulnerability Management
Detecting outdated systems and misconfigured SSL certificates.
Brand Protection
Monitoring mentions, reputation issues, and impersonation risks.
Digital Footprint Monitoring
Tracking an organization’s exposed information across the internet.
Incident Response
Collecting quick intelligence on a compromised host or suspicious domain.
Conclusion
SpiderFoot integrates with one of the largest collections of OSINT data sources available in any automated intelligence tool. Its modules span DNS records, search engines, breach databases, social intelligence, malware feeds, geolocation services, SSL logs, metadata extractors, and many more. SpiderFoot creates an interconnected web of intelligence that offers unparalleled visibility into digital footprints and online exposures.
SpiderFoot provides powerful automation, deep scanning capabilities, and multi-layered analysis, making it a preferred OSINT solution for cybersecurity professionals worldwide. With hundreds of modules working together, it transforms raw data into meaningful insight, enabling users to make accurate and informed decisions in their security strategies.