SpiderFoot is widely known as one of the most powerful open-source OSINT automation tools available today. It is used by cybersecurity professionals, penetration testers, investigators, and researchers who need rapid and reliable intelligence gathering. But one question many new users ask is whether SpiderFoot demands advanced technical expertise to operate successfully. This question becomes even more important for beginners who are exploring OSINT for the first time.
SpiderFoot provides exceptional depth, automation, and flexibility, yet not every feature requires expert-level knowledge. The tool is designed to support both new and highly skilled users by offering a clean web interface, automated scanning workflows, and customizable modules. This article explores in detail whether SpiderFoot requires advanced technical skills, how it works for different user levels, and what aspects may or may not require deeper technical understanding.
Understanding SpiderFoot as an OSINT Automation Tool
SpiderFoot is primarily built to simplify the tedious and repetitive tasks involved in OSINT data collection. Traditionally, reconnaissance requires manually gathering information from dozens of sources such as DNS records, WHOIS databases, social networks, IP lookups, breach databases, and much more. SpiderFoot automates almost all of these tasks through its modular engine.
The design principle behind SpiderFoot is that users should spend less time collecting data and more time analyzing it. This is why it integrates with a wide range of data sources, provides dynamic scanning workflows, and offers both a graphical interface and command-line functionality.
While SpiderFoot is rich in features, its usability depends on the user’s familiarity with OSINT concepts. The interface itself is simple, but interpreting results sometimes requires technical thinking. However, the tool is not restricted to experts only; rather, it scales according to the user’s expertise.
The Learning Curve for New Users
For beginners, SpiderFoot does not impose an overwhelming learning burden. Most new users can start conducting basic scans within minutes. The web interface guides them step by step, from entering a target to selecting modules and launching the scan. The tool’s automation ensures that users are not required to manually interact with data sources.
However, beginners may initially struggle with understanding the technical meaning of certain modules or interpreting results. For example, understanding DNS output, understanding open ports, recognizing network subnets, or interpreting breach data may require basic cybersecurity knowledge. But this is not SpiderFoot’s limitation; it is a natural part of OSINT itself.
The interface presents findings in an organized way, which helps new learners understand patterns over time. With continued use, even non-technical users can quickly become comfortable with the tool’s workflows.
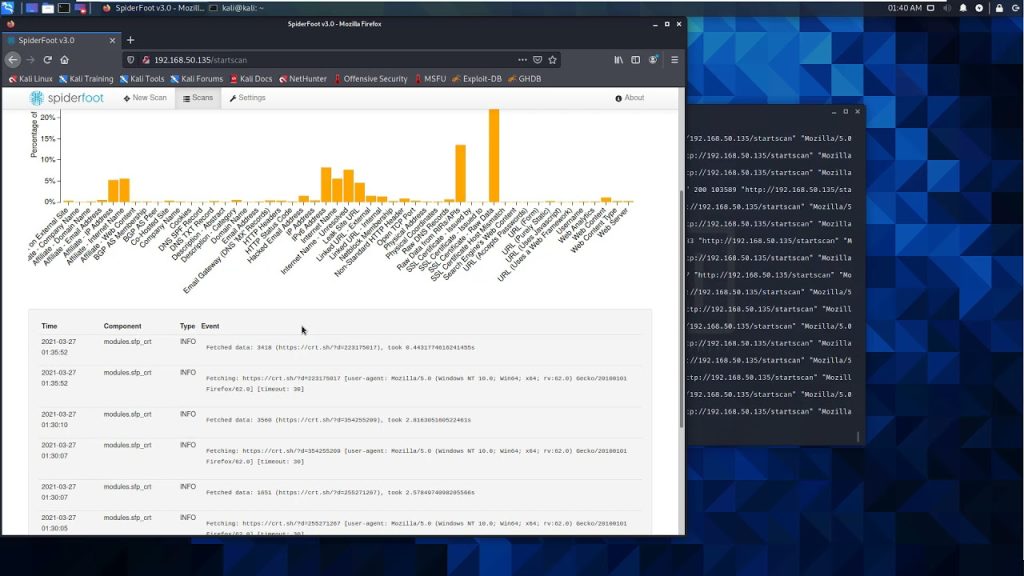
How the Graphical Web Interface Lowers Technical Barriers
One of the strongest advantages of SpiderFoot is its built-in web interface, which significantly lowers the technical skill requirement. Users who are unfamiliar with command-line operations can still run complete OSINT investigations using only the graphical environment.
The web interface includes:
• Clear navigation menus
• Simple forms for setting scan parameters
• Visual charts and organized results
• Module selection through checkboxes
• Automatic grouping of collected intelligence
Because of this, even someone with minimal cybersecurity experience can use SpiderFoot to gather actionable intelligence. The interface provides explanations for modules and settings, which further reduces complexity.
In contrast, many traditional OSINT tools rely heavily on terminal commands or manual API interactions. SpiderFoot removes those barriers by offering a friendly UI designed for all user levels.
Running SpiderFoot from the Command Line
While the web interface is ideal for beginners, SpiderFoot also offers a command-line interface (CLI) that appeals to advanced users. This mode is beneficial for automation, scripting, remote usage, or integration with workflows. The CLI requires at least moderate technical knowledge because it involves command syntax, parameters, and sometimes scripting.
For example, expert users may:
• Automate repeated scans using scripts
• Integrate SpiderFoot into penetration testing pipelines
• Combine its output with other analysis tools
• Run it on remote servers with limited system resources
These tasks require comfort with Python, shells, and network concepts. Therefore, while basic usage is beginner-friendly, advanced usage definitely requires technical expertise. This dual-mode functionality makes SpiderFoot versatile, catering to both entry-level and professional users.
Understanding Modules and Their Technical Complexity
SpiderFoot contains a vast number of modules designed for different purposes. Some modules are simple and easy to understand, while others require deeper technical knowledge. The complexity depends on the nature of the data being collected.
Examples of simple modules include:
• WHOIS lookups
• Email address enumeration
• Social media checks
• Basic DNS record collection
These are understandable by most users, even with limited technical background.
More advanced modules may involve:
• ASN lookups
• Network block mapping
• Port scanning and service detection
• Metadata extraction
• Deep breach analysis
Understanding the output of these modules may require intermediate or advanced technical knowledge. SpiderFoot does not hide the raw data; instead, it organizes it clearly, but interpretation depends on the user’s skill level.
Interpreting SpiderFoot Results: Does It Require Expertise?
Interpreting results is an area where technical skill can make a difference. The tool collects large volumes of intelligence from multiple data sources. While the interface organizes information into categories, the user must determine what is relevant or important.
For example:
• Recognizing errors in DNS configurations
• Identifying exposed services
• Validating suspicious IP ranges
• Detecting risky digital footprints
• Understanding correlation between data points
These tasks become easier with technical experience. A beginner may see the results as information, but an expert sees them as actionable insights. However, SpiderFoot does not require users to interpret everything manually; it highlights relationships, connections, and alerts that simplify the process.
SpiderFoot Automation: Reducing the Need for Manual Skills
A key feature that reduces technical skill requirements is automation. SpiderFoot automates data collection, scanning, and reporting, eliminating the need for users to manually query dozens of sources.
Automation includes:
• Running modules without user intervention
• Collecting data from multiple APIs
• Correlating and cross-referencing findings
• Flagging suspicious results
• Organizing outputs into neat categories
Because of this automation, even beginners can perform complex OSINT investigations without mastering the underlying technologies.
Advanced users can still customize automation flows, but basic usage requires minimal effort. This is one of the reasons SpiderFoot is popular among students, researchers, and even journalists exploring OSINT.
Use Cases for Beginners
SpiderFoot is accessible to entry-level users who need:
• Simple reconnaissance
• Domain information checks
• Social media or email intelligence
• Exposure monitoring
• Basic OSINT practice
• Understanding digital footprints
Beginners can start with default settings, relying on SpiderFoot’s automation to gather and present information. The minimal technical requirement makes it an excellent learning tool.
Use Cases for Intermediate Users
Intermediate users typically have some prior experience with cybersecurity or OSINT. SpiderFoot suits them well because they can:
• Select specific modules for targeted scans
• Interpret more complex results
• Conduct structured investigations
• Combine output with other security tools
• Understand network-based findings
This category of users benefits greatly from SpiderFoot’s modular flexibility.
Use Cases for Advanced Professionals
Advanced users such as penetration testers, threat analysts, and digital forensic experts leverage SpiderFoot’s full potential. They may:
• Build custom scanning workflows
• Use command-line automation
• Integrate SpiderFoot with external tools
• Create custom modules
• Analyze technical results at a deep level
While the tool supports experts, it does not force beginners to learn advanced features. This layered structure is one of SpiderFoot’s biggest strengths.
Does SpiderFoot Require Coding Knowledge?
For basic usage, SpiderFoot does not require any coding skills. Users can run scans entirely through the interface without writing scripts or modifying code.
For advanced customization, coding knowledge may be useful, particularly in:
• Writing custom modules
• Automating scans using scripts
• Modifying the framework
• Integrating with external APIs
But again, this level of skill is optional, not mandatory.
Does SpiderFoot Require Networking Knowledge?
To get the most value from SpiderFoot, having some understanding of network technologies helps. For example:
• DNS
• IP ranges
• Subnets
• Web services
• Ports and protocols
However, SpiderFoot does not require mastery of these concepts. Beginners can still collect and interpret basic information using the interface.
How SpiderFoot Helps Both Non-Technical and Technical Users
SpiderFoot’s design makes it suitable for both non-technical and technical users:
Non-technical users benefit from:
• A clean web interface
• Automated scanning
• Simple navigation
• Organized results
Technical users benefit from:
• Command-line options
• Custom modules
• Integration capabilities
• Flexible configurations
This dual appeal makes SpiderFoot a widely adopted OSINT tool across industries.
Conclusion
SpiderFoot is highly versatile, and its usability does not depend strictly on advanced technical skills. Beginners can operate it effectively using the web interface and automated scanning features, while intermediate and advanced users can leverage deeper configurations to perform complex investigations. The tool adapts to the user’s skill level, allowing anyone to conduct meaningful OSINT research without being overwhelmed by complexity. Whether used for security assessments, reconnaissance, or digital footprint analysis, SpiderFoot provides a balanced environment suitable for all technical backgrounds.